Book your demo
CloudNine has acquired ESI Analyst and are looking forward to working with you.
Click here to request a demo of CloudNine’s ESI Analyst

CloudNine has acquired ESI Analyst and are looking forward to working with you.
Click here to request a demo of CloudNine’s ESI Analyst

In our previous article we touched on how the digital breadcrumbs of our information age are sparking a new era of criminal investigations. Corporations have also seized upon this wealth of information driven by our digital information era, amassing vast amounts of data allowing them to target consumers with laser-focused precision. The same can be done with electronically stored information (ESI) in the context of civil litigation and discovery.
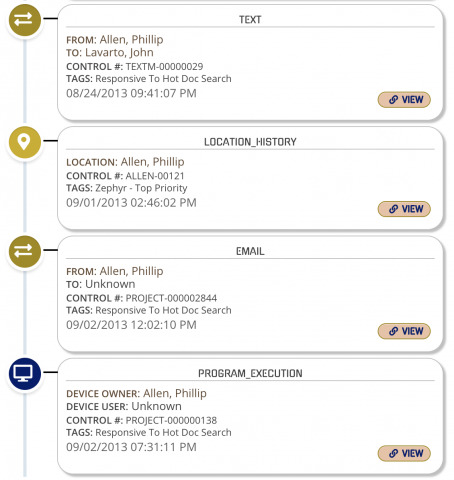
If you are focused solely on traditional document-based electronic discovery, you may be missing a plethora of potential evidence represented by the numerous digital breadcrumbs one leaves behind. Let’s walk through an example timeline that for all intents and purposes would be considered the innocent digital history of a business traveler.
Our traveler is an employee of a large corporation that delivers widgets to their clients. The pricing for these widgets is highly confidential, and something that is sought after by their competition. Here is an example timeline of digital breadcrumbs extracted from her smartphone and laptop.
5:03 PM PT: Our traveler checks in for a flight to San Francisco using her airline’s mobile app. Subsequently creating her digital boarding pass and storing it in her smartphone's wallet app.
5:25 PM PT: She maps her route to the airport. Perhaps she does not know the way to the airport from her current location, or it could be because she wants to see traffic and determine her ETA.
5:42 PM PT: She sends a text message to a colleague letting him know that she will be arriving later that evening, and that they should grab a drink if he has time to review the pending meeting and proposal. They subsequently exchanged several text messages until 5:58 PM PT, some of them include emojis.
6:12 PM PT: Our traveler begins her drive to the airport with her map application providing a familiar voice telling her to turn left at the stoplight, and then take the upcoming right turn at the next.
6:17 PM PT: Perhaps bored with the silence of her drive, our traveler fires up Spotify and begins to play some of her favorite music.
If you are focused solely on traditional document-based electronic discovery, you may be missing a plethora of potential evidence represented by the numerous digital breadcrumbs one leaves behind.
6:41 PM PT: She arrives at the valet parking facility near the airport, jumps in the airport shuttle and begins to make her way to the terminal. Along the way she opens Facebook and comments on a friend’s recent post.
6:56 PM PT: About the time the bus arrives to the terminal, our traveler opens up her flight app to check her flight’s status, and in doing so sets up an alert, as flights to San Francisco are often delayed.
7:04 PM PT: She receives her first notification that her flight has been delayed. This prompts an update to her colleague in San Francisco explaining that she may not be able to meet, as it looks like things are getting pushed back a bit. He responds with multiple sad-faced emojis.
7:29 PM PT: Another flight update alert pops up telling her that her flight time has been updated, and her gate has changed.
7:45 PM PT: Feeling tired, she purchases coffee using her preloaded Starbucks card located in her smartphone's wallet app.
8:04 PM PT: She opens an email from her firm’s client and responds with a brief update surrounding the next day’s meeting time noting her flight delay, as well as wishing them a nice evening.
8:09 PM PT: Knowing her likely late arrival, she logs into her hotel app and checks the status of her room. To ensure she doesn’t lose her reservation due to her anticipated late arrival, she checks in via the app and requests a digital room key.
8:13 PM PT: Not wanting to waste the evening, she opens her laptop and begins updating the draft proposal for her meeting. She saves the updated draft at 8:44 PM PT to a USB drive that she then removes and drops into her laptop bag.
8:22 PM PT: A text message pops up in her notifications telling her that her flight is now boarding and provides the gate information. She then makes her way to the gate, relieved that she is finally on her way.
8:47 PM PT: She fires off one last text message prior to turning off her electronic devices to inform her colleague that she is now on her way, and if he is still willing, they could meet in the hotel lobby later that evening.
11:03 PM PT: Opening the Uber app, our traveler requests a car and inputs the address of the hotel as her destination.
11:12 PM PT: She sends one last text message to her colleague stating that she is on her way to the hotel from the airport.
11:21 PM PT: She receives a text message from her colleague stating he is at the bar of the hotel and will meet her there.
All of the above are digital breadcrumbs that provide context to our traveler’s evening. On the surface, all of these events seem innocuous. However, what if the colleague she was meeting was suspected of stealing trade secrets from her company? What if the changes to the proposal saved from her laptop to that USB drive were critical to proving these allegations? What if this proposal detailed the new widget pricing her company was trying so hard to protect?
We will dive into how this evidence could be critical to solving the mystery in our next article. In the meantime, if you are seeking a collaborative and cost-effective way to assemble a timeline of digital evidence like the one in our example, perhaps check out a demonstration of ESI Analyst.
© 2018 - 2021 ~ TIDAL CHANGE TECHNOLOGIES, INC. ~ ALL RIGHTS RESERVED
CloudNine has acquired ESI Analyst and are looking forward to working with you.
Click here to request a demo of CloudNine’s ESI Analyst